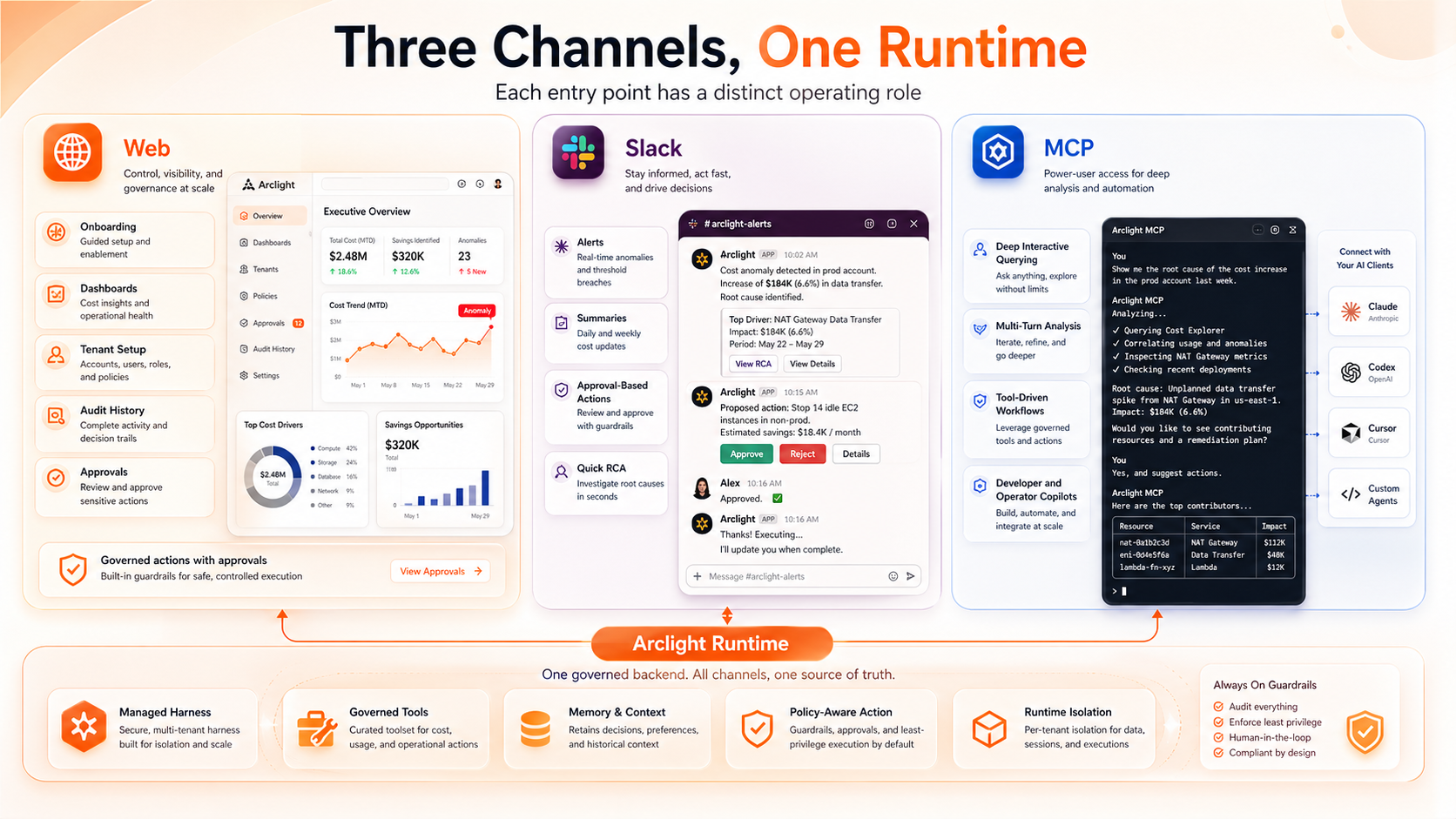
Web Workspace
Onboarding, dashboards, AWS account setup, tenant configuration, approval queues, and audit history.
Arclight
Arclight gives finance, platform, and operations teams one interactive runtime for AWS cost questions, anomaly analysis, recommendations, approval workflows, and governed remediation.
Interaction Model
Onboarding, dashboards, AWS account setup, tenant configuration, approval queues, and audit history.
Alerts, summaries, quick RCA, cleanup proposals, approval buttons, and execution receipts in the team workflow.
Connect Claude, Codex, Cursor, and custom agents to a governed Arclight runtime for deeper multi-turn investigation.
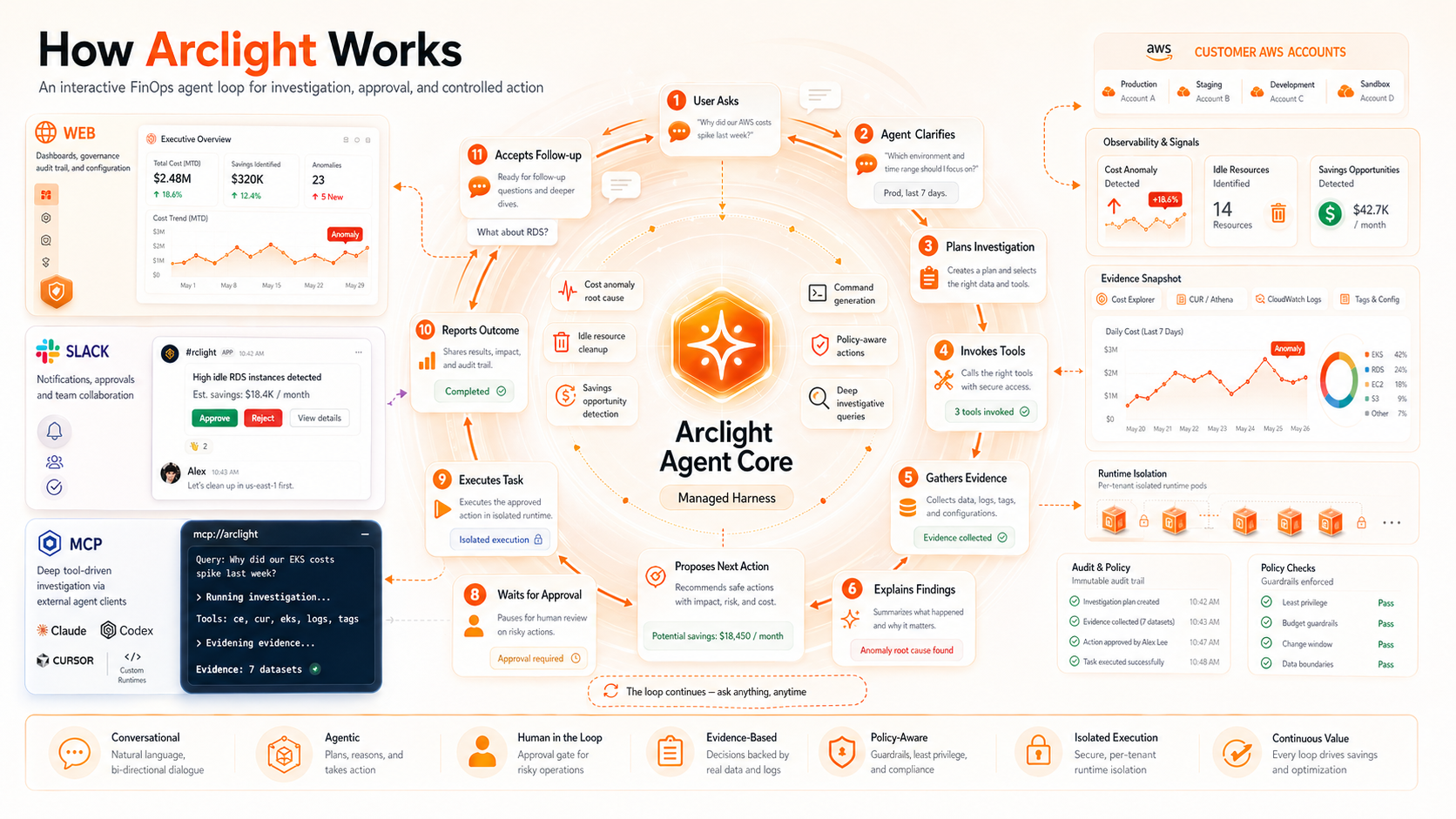
Agent Loop
A user asks a cost question, Arclight clarifies intent, plans the investigation, invokes AWS billing and operational tools, gathers evidence, explains the finding, proposes action, waits for approval when needed, executes, and reports the result.
Capability Landscape
Cost anomaly RCA, service-level drivers, account spikes, resource inventory, and evidence trails.
Idle resources, unused reservations, underutilized compute, storage waste, and unexpected usage changes.
Rightsizing, cleanup, lifecycle policies, reserved capacity options, and architecture improvement paths.
Monthly run-rate, budget risk, expected savings, seasonal patterns, and optimization impact estimates.
Approval-gated cleanup, tagging changes, snapshot review, non-production shutdown, and controlled remediation.
Audit history, tenant isolation, policy guardrails, permission boundaries, and change traceability.

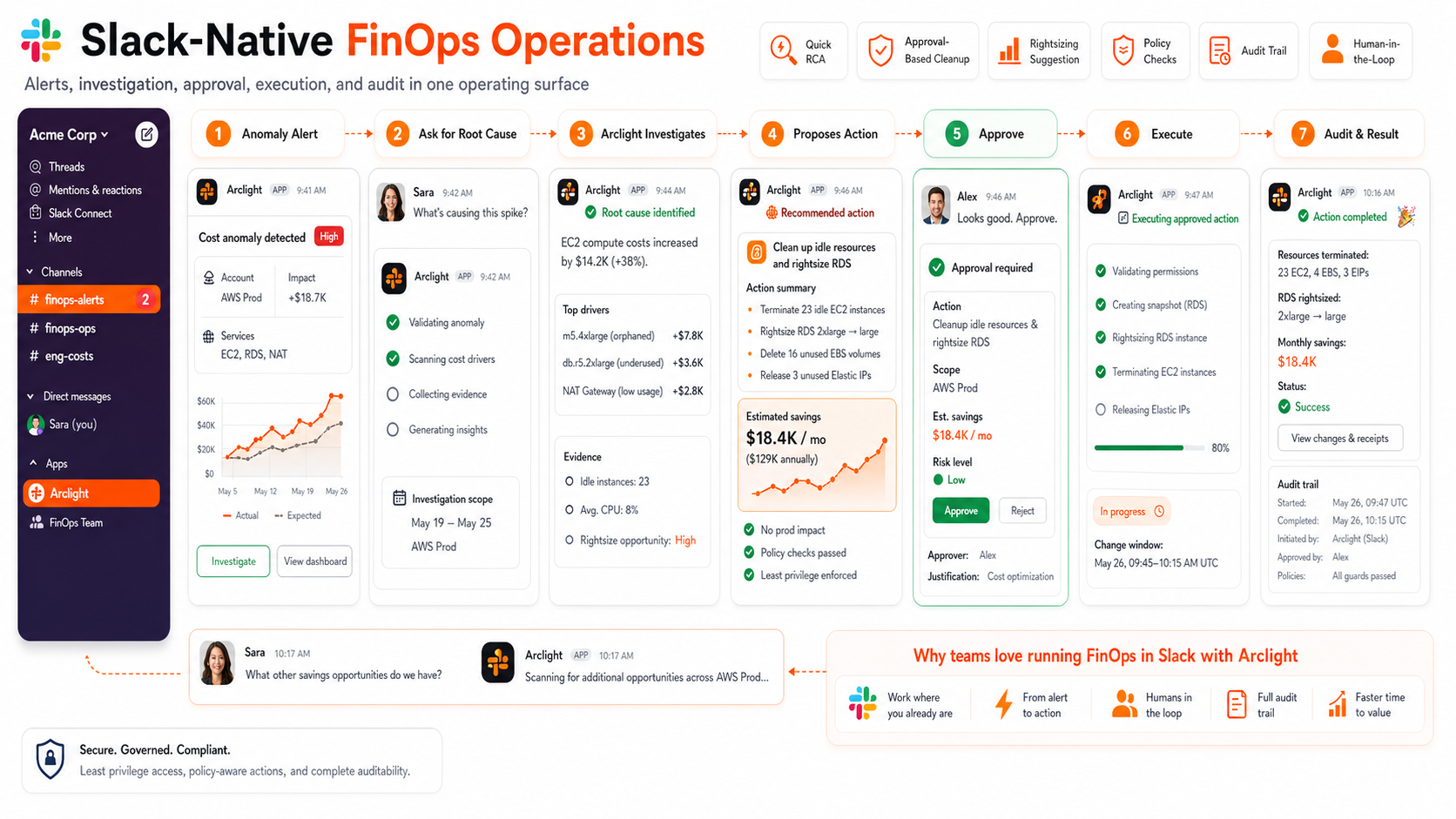
Slack
Arclight can post a cost anomaly alert, answer follow-up questions, investigate root cause, propose cleanup or rightsizing, wait for approval, execute a controlled action, and post the audit result.
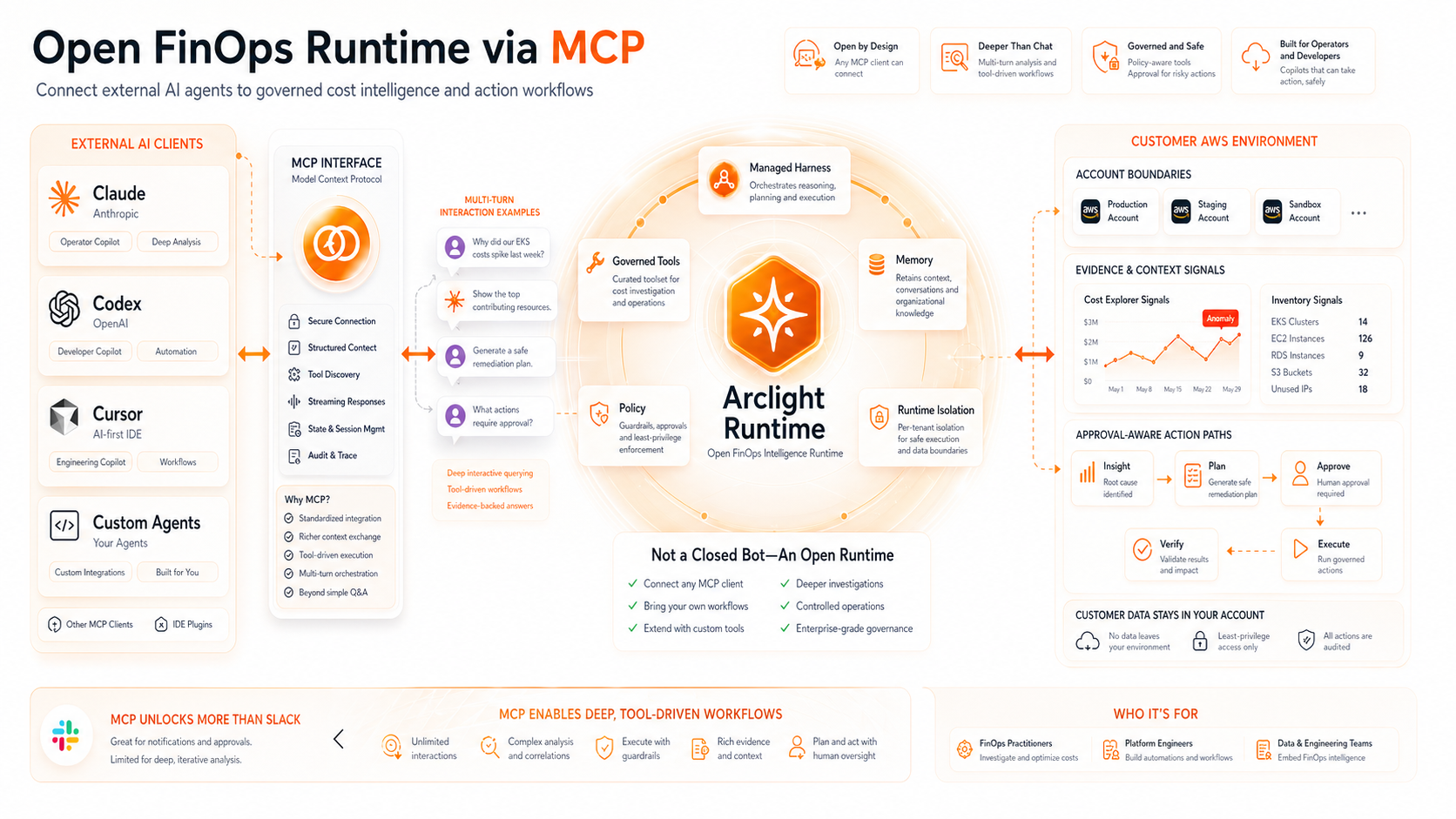
MCP
MCP lets external AI clients connect to Arclight, use governed tools, and run deeper interactive investigations without turning Arclight into a closed chat bot.
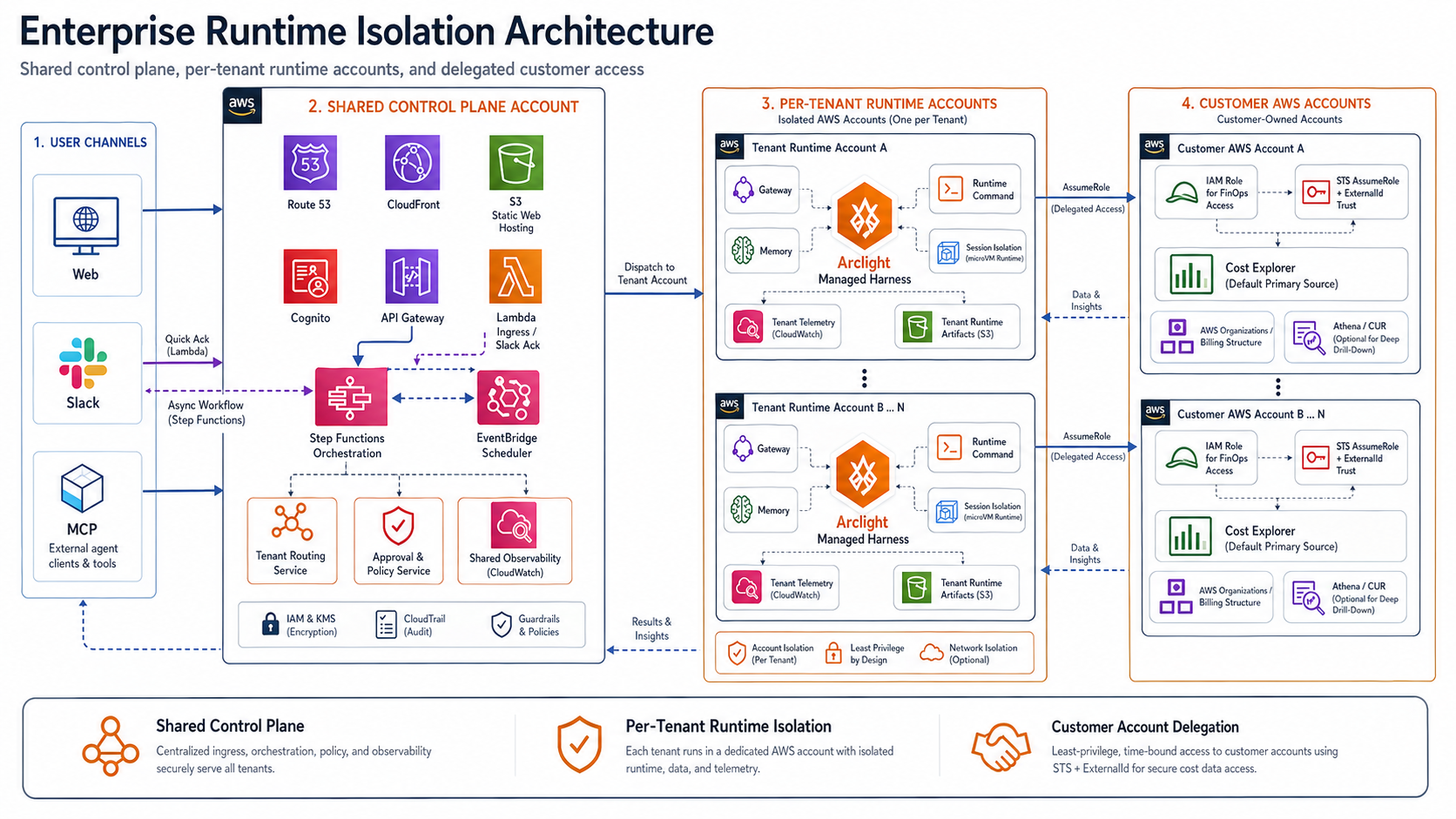
Enterprise Runtime Isolation
The target architecture uses a shared control plane with per-tenant runtime accounts, delegated customer access, role assumption boundaries, audit logging, and approval gates for actions that can change infrastructure.
Pilot